1. Which two commands should be implemented to return a Cisco 3560 trunk port to its default configuration? (Choose two.)
S1(config-if)# switchport mode access
S1(config-if)# switchport access vlan 1
S1(config-if)# no switchport trunk native vlan
S1(config-if)# no switchport trunk allowed vlan
S1(config-if)# switchport mode dynamic desirable
2. Which command will enable auto-MDIX on a device?
S1(config-if)# mdix auto
S1# auto-mdix
S1(config-if)# auto-mdix
S1# mdix auto
S1(config)# mdix auto
S1(config)# auto-mdix
3. Which three parameters could be in an extended access control list? (Choose three.)
access list number between 1 and 99
default gateway address and wildcard mask
destination address and wildcard mask
source address and wildcard mask
access list number between 100 and 199
subnet mask and wild card mask
4. Fill in the blank.
The OSPF Type 1 packet is the hello packet.
5. The computers used by the network administrators for a school are on the 10.7.0.0/27 network. Which two commands are needed at a minimum to apply an ACL that will ensure that only devices that are used by the network administrators will be allowed Telnet access to the routers? (Choose two.)
access-list 5 deny any
ip access-group 5 in
access-list 5 permit 10.7.0.0 0.0.0.31
ip access-group 5 out
access-list standard VTY
permit 10.7.0.0 0.0.0.127
access-class 5 in
the all-link router multicast
the all OSPF router multicast
the global unicast of the interface
the link-local address of the interface
7. Why would an administrator use a network security auditing tool to flood the switch MAC address table with fictitious MAC addresses?
to determine which ports are not correctly configured to prevent MAC address flooding
to determine if the switch is forwarding the broadcast traffic correctly
to determine which ports are functioning
to determine when the CAM table size needs to be increased in order to prevent overflows
8. Which two statements are true about half-duplex and full-duplex communications? (Choose two.)
All modern NICs support both half-duplex and full-duplex communication.
Full duplex increases the effective bandwidth.
Full duplex offers 100 percent potential use of the bandwidth.
Full duplex allows both ends to transmit and receive simultaneously.
Half duplex has only one channel.
9.
Refer to the exhibit. A network administrator has just configured address translation and is verifying the configuration. What three things can the administrator verify? (Choose three.)
A standard access list numbered 1 was used as part of the configuration process.
Three addresses from the NAT pool are being used by hosts.
Address translation is working.
One port on the router is not participating in the address translation.
The name of the NAT pool is refCount.
Two types of NAT are enabled.
10. A network administrator is implementing a distance vector routing protocol between neighbors on the network. In the context of distance vector protocols, what is a neighbor?
routers that share a link and use the same routing protocol
routers that exchange LSAs
routers that reside in the same area
routers that are reachable over a TCP session
11. Which two methods can be used to provide secure management access to a Cisco switch? (Choose two.)
Configure all switch ports to a new VLAN that is not VLAN 1.
Configure all unused ports to a “black hole.”
Configure SSH for remote management.
Configure specific ports for management traffic on a specific VLAN.
Configure the native VLAN to match the default VLAN.
DNS, unicast
PING, multicast
ARP, multicast
PING, broadcast
DNS, broadcast
ARP, broadcast
lineconin
14. A logical topology influences the type of network framing and media access control that will be used.
15. Which two statements describe the characteristics of fiber-optic cabling? (Choose two.)
Fiber-optic cabling uses LEDs for single-mode cables and laser technology for multimode cables.
Fiber-optic cabling does not conduct electricity.
Fiber-optic cabling has high signal loss.
Fiber-optic cabling is primarily used as backbone cabling.
Multimode fiber-optic cabling carries signals from multiple sending devices.
16. Which two protocols function at the internet layer? (Choose two.)
ARP
ICMP
BOOTP
PPP
IP
17. Which firewall technique blocks incoming packets unless they are responses to internal requests?
URL filtering
port filtering
application filtering
stateful packet inspection
18. Consider the following range of addresses:
2001:0DB8:BC15:00A0:0000::
2001:0DB8:BC15:00A1:0000::
2001:0DB8:BC15:00A2:0000::
2001:0DB8:BC15:00AF:0000::
The prefix-length for the range of addresses is /60.
19 What three application layer protocols are part of the TCP/IP protocol suite? (Choose three.)
FTP
ARP
NAT
DHCP
PPP
DNS
20 Which communication tool allows real-time collaboration?
weblog
wiki
e-mail
instant messaging
21 Which of the following are primary functions of a router? (Choose two.)
packet switching
microsegmentation
flow control
path selection
domain name resolution
22 TFRP is a best-effort, connectionless application layer protocol that is used to transfer files.
23
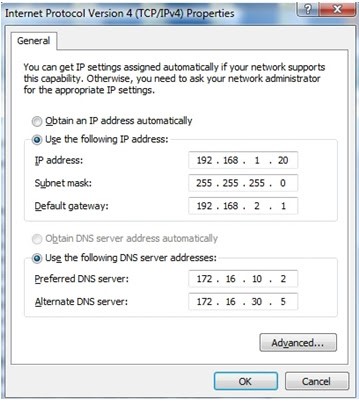
Can not connect to webpages, dns is ok.
Issue is: Default Gateway.
24
It will give 4 options about ping, the correct one is: The PC2 will be able to ping 192.168.1.1
25
The question is from where is the system image being loaded. Answer: flash.
26
It will ask what is the issue.
Answer is:
The user has to be in privileged EXEC mode to use that command.
27. What are three characteristics of multicast transmission? (Choose three.)
A single packet can be sent to a group of hosts.
Multicast messages map lower layer addresses to upper layer addresses.
Multicast transmission can be used by routers to exchange routing information.
Computers use multicast transmission to request IPv4 addresses.
The source address of a multicast transmission is in the range of 224.0.0.0 to 224.0.0.255.
28 At a minimum, which address is required on IPv6-enabled interfaces?
global unicast
link-local
site local
unique local
29 Which frame forwarding method receives the entire frame and performs a CRC check to detect errors before forwarding the frame?
fragment-free switching
fast-forward switching
store-and-forward switching
Descargar el exámen
Espero haber ayudado en algo. Hasta la próxima oportunidad!
Twittear





No hay comentarios:
Publicar un comentario